ISO/IEC 27001 provides requirements for an information security management system (ISMS), though there are more than a dozen standards in the ISO/IEC 27000 family. Using them enable organizations to manage the security of assets such as financial information, intellectual property, employee details or information entrusted by third parties.
The full name of the ISO 27000 family is passed as ISO / IEC 27000 and is published by the ISO (International Organization for Standardization) and IEC (International Electrotechnical Commission).
ISO/IEC 27001:2013 specifies the requirements for establishing, implementing, maintaining and continually improving an information security management system within the context of the organization. It also includes requirements for the assessment and treatment of information security risks tailored to the needs of the organization. The requirements set out in ISO/IEC 27001:2013 are generic and are intended to be applicable to all organizations, regardless of type, size or nature.
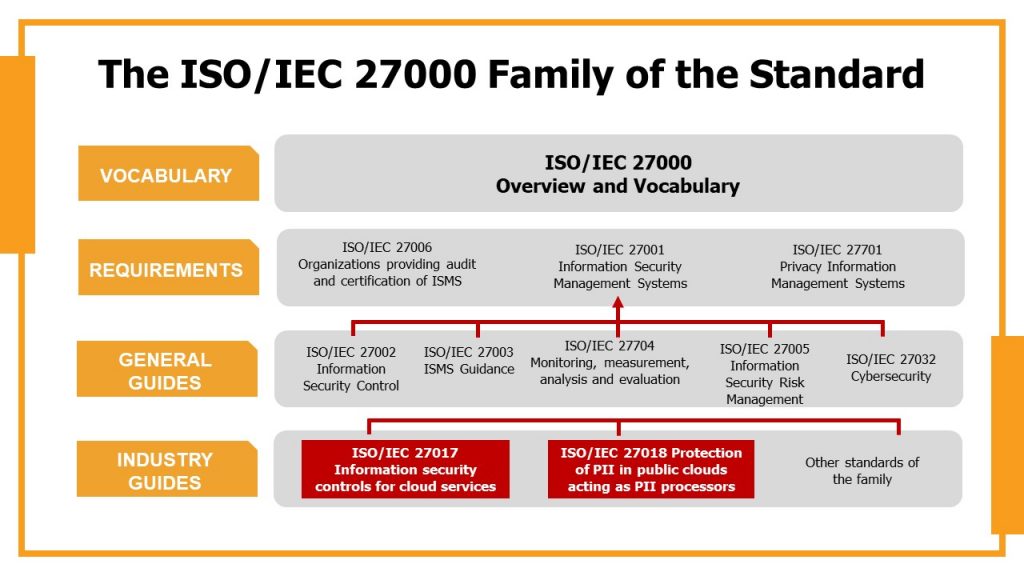
ISO/IEC 27000:2018 Overview and vocabulary
ISO/IEC 27000:2018 provides the overview of information security management systems (ISMS). It also provides terms and definitions commonly used in the ISMS family of standards. This document is applicable to all types and sizes of organization.
ISO/IEC 27006:2015 Requirements for bodies providing audit and certification of information security management systems
ISO/IEC 27006:2015 specifies requirements and provides guidance for bodies providing audit and certification of an information security management system (ISMS), in addition to the requirements contained within ISO/IEC 17021‑1 and ISO/IEC 27001. It is primarily intended to support the accreditation of certification bodies providing ISMS certification.
The requirements contained in this International Standard need to be demonstrated in terms of competence and reliability by anybody providing ISMS certification, and the guidance contained in this International Standard provides additional interpretation of these requirements for anybody providing ISMS certification.
ISO/IEC 27701:2019 Privacy information management System
This document specifies requirements and provides guidance for establishing, implementing, maintaining and continually improving a Privacy Information Management System (PIMS) in the form of an extension to ISO/IEC 27001 and ISO/IEC 27002 for privacy management within the context of the organization.
This document specifies PIMS-related requirements and provides guidance for PII controllers and PII processors holding responsibility and accountability for PII processing.
This document is applicable to all types and sizes of organizations, including public and private companies, government entities and not-for-profit organizations, which are PII controllers and/or PII processors processing PII within an ISMS.
ISO / IEC 27002: 2013 Information security controls
ISO / IEC 27002: 2013 gives guidelines for organizational information security standards and information security management practices, including the selection, implementation and management of controls, taking into account the organization’s information security risk environments. That is to say; Choosing controls in the process of implementing an Information Security Management System based on ISO / IEC 27001, implementing widely accepted information security controls, developing its own information security management guidelines.
> ISO/IEC 27003:2017 provides explanation and guidance on ISO/IEC 27001
ISO / IEC 27005: 2018 Information security risk management
This document provides guidelines for information security risk management. It supports the general concepts outlined in ISO / IEC 27001 and is designed to assist in the satisfactory implementation of information security based on a risk management approach.
Knowledge of the concepts, models, processes and terminologies described in ISO / IEC 27001 and ISO / IEC 27002 is essential for a thorough understanding of this document. It applies to all types of organizations that aim to manage risks that may endanger the organization’s information security.
ISO/IEC 27032:2012 Cybersecurity
ISO/IEC 27032:2012 provides guidance for improving the state of Cybersecurity, drawing out the unique aspects of that activity and its dependencies on other security domains, in particular:
· information security,
· network security,
· internet security, and
· critical information infrastructure protection (CIIP).
It covers the baseline security practices for stakeholders in the Cyberspace.
ISO/IEC 27017:2015 Information security controls for cloud services
ISO/IEC 27017:2015 gives guidelines for information security controls applicable to the provision and use of cloud services by providing: additional implementation guidance for relevant controls specified in ISO/IEC 27002, additional controls with implementation guidance that specifically relate to cloud services.
ISO/IEC 27018:2019 Protection of personally identifiable information (PII) in public clouds acting as PII processors
This document sets out widely accepted control objectives, controls and guidelines for implementing measures to protect Personally Identifiable Information (PII) in line with the privacy principles in ISO / IEC 29100 for the public cloud computing environment. It specifies guidelines based on ISO / IEC 27002, taking into account the legal requirements for the protection of PII that can be applied in the context of the public cloud services provider’s information security risk environments. It applies to all types and sizes of organizations, including public and private companies, government agencies and non-profit organizations that provide information processing services as PII processors through cloud computing to other organizations on a contractual basis.








